The cloud is incredibly useful, so it’s no wonder criminals are using cloud computing to make their operations more efficient.
Unfortunately, this means we’re all at risk.
Cloud computing is just too important to stop using though, so how can you prevent the criminals and protect yourself with cloud computing data security?
Why are Criminals Using Cloud Computing?
Criminals are using cloud computing for exactly the same reasons legitimate users are. Namely, it’s an excellent way to share information and capabilities.

This makes the process more efficient, allowing criminal gangs to maximize income from online activities.
- It provides easy access to information: There are many different parts to online crime, but most of it begins with access to compromised credentials. The cloud allows criminals to share these data logs more efficiently, reducing the time it takes to identify valuable targets.
- It enables people to specialize: As with most lines of work, cybercriminals also have areas of specialization. Some might specialize in ransomware, others phishing, others stealing crypto, etc. They each need access to different vulnerabilities, and cloud computing enables them to find this more effectively.
- It makes the process quicker: easy access to information means cybercriminals can carry out attacks more quickly, giving enterprises less time to respond.
- It allows for more attacks: By speeding up the process, criminals using cloud computing can carry out more attacks, making them more money.
As you can see, these are some pretty compelling reasons for criminals to use cloud computing.
Security Issues in Cloud Computing
Not only does cloud computing help cybercriminals improve their processes, but it also gives them access to the vital data they need to carry out their attacks.
Security issues exist in computing: it’s a fact of modern life.
Cloud computing is a safe way to store data, but it’s not without its security issues.
Misconfiguration
The cloud is designed to make it simple for people within an organization to share information. The difficulty is limiting to what extent information should be shared.
Not every piece of information should be available to everyone in the organization, and the more hands it touches, the more vulnerable it becomes. This is why an important part of our initial and ongoing networks assesments are focused on reviwing access and putting processes in place to control that access.
Cloud computing places some of the responsibility for security on the cloud service provider, but businesses still need to be able to properly configure their security settings.
Login Credentials
Many businesses and employees still aren’t good about password security.
When login credentials become compromised, this gives criminals access to huge amounts of data contained on the cloud.
This is made even worse by the fact that many people reuse passwords and usernames. Once one account becomes compromised, all the other ones do as well, giving the hacker even more opportunities to do damage.
External Sharing of Data
One of the reasons for criminals using cloud computing to find security weaknesses is this idea of sharing. Sharing is a necessary part of collaboration, but it’s also a weakness when it comes to security.
What happens when you tell your friend a juicy piece of gossip? You have no way to know where it will get to.
When you share documents in the cloud using links it’s a similar story. If you don’t set the right permissions, this information can be forwarded on and it’s very difficult to keep track of who has access to it.
If you’re working with sensitive data, this can make you very vulnerable.
Malicious Insiders
It’s not just people on the outside that you need to worry about. Sometimes there are malicious insiders within your own organization that can cause severe damage.
It might be a disgruntled employee, someone who is being paid by a rival, or any number of reasons.
The thing is, if you don’t have your cloud computing set up properly, then these people have access to an incredible amount of information. For this reason, you need to maintain close oversight over who has access to what.
The cloud should give people access to the information they need and limit access to everything else.
Lack of Training
Internet security is complicated. Your employees don’t need to know the technical details of how it works, but they do need basic knowledge.
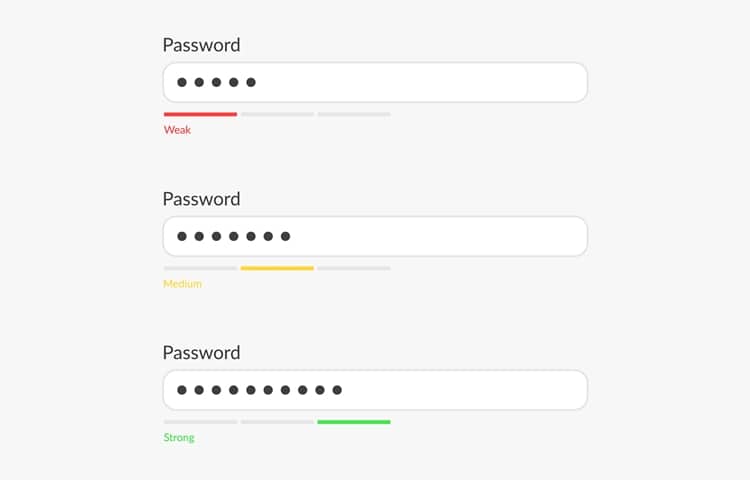
Understanding why it’s important to use strong passwords and two-factor authentication, taking extra precautions when using public networks; these are the kinds of things that can make a big difference to your online security.
Our security Awarness Training on these things can go a long way to protecting your business.
Conclusion: Criminals Using Cloud Computing
Not only are criminals using cloud computing to improve their malicious activities, but they’re also using it to identify weaknesses in your security.
If your cloud security isn’t set up properly, then your information is at risk.
It’s time to take security issues in cloud computing seriously.

